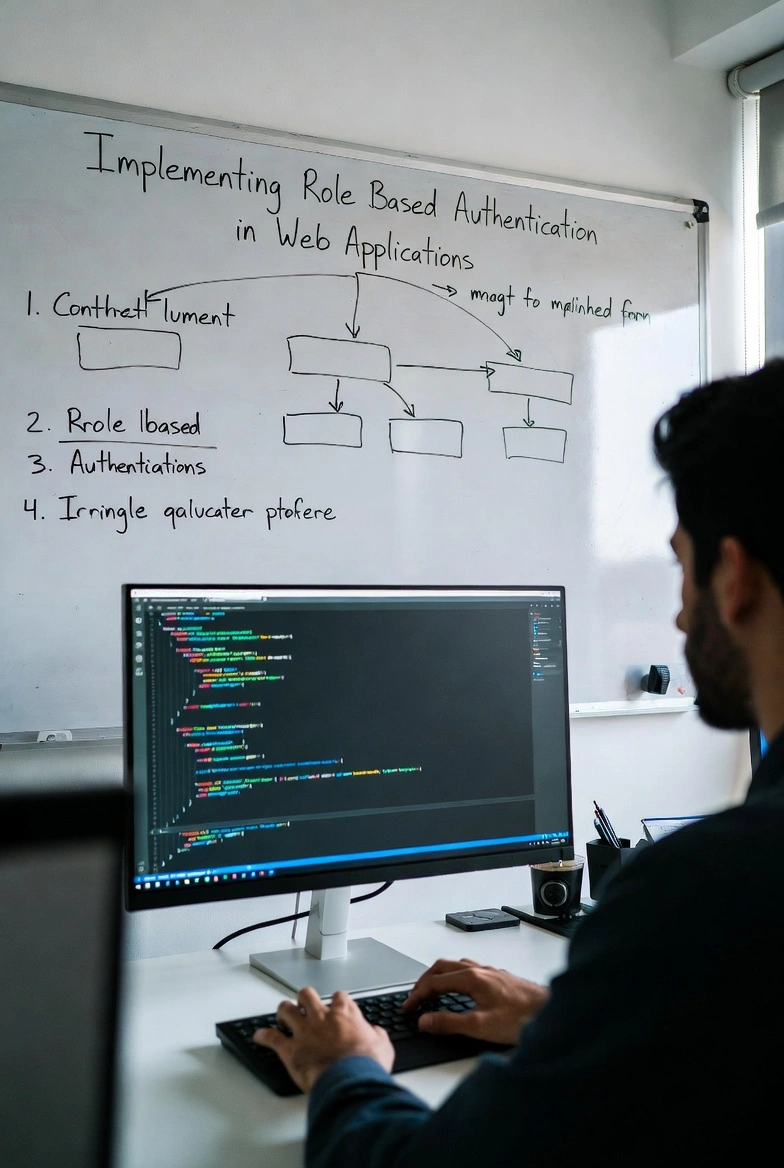
Role based authentication is a critical security strategy for modern web applications. As systems grow in complexity organizations must control how users interact with data features and administrative tools. A structured role based model ensures that each user receives appropriate access according to defined responsibilities. When implemented correctly this approach improves security strengthens compliance and simplifies long term maintenance.
1. Understanding Role Based Authentication
Defining Roles and Permissions
Role based authentication operates on the principle that users are assigned roles and roles are associated with permissions. Instead of assigning permissions directly to individual users the system maps capabilities to predefined roles such as administrator editor or viewer.
This model reduces management overhead. When responsibilities change administrators only update the role rather than modifying every individual account. This structure also minimizes configuration errors that could expose sensitive data.
Benefits of Access Control Modeling
A structured access control model improves accountability. Each action within the application can be traced back to a defined role which enhances audit processes and regulatory compliance.
Additionally centralized role management simplifies onboarding and offboarding procedures. New employees can be granted access instantly by assigning an existing role which accelerates operational efficiency while maintaining security integrity.
2. Designing a Secure Authorization Architecture
Authentication Versus Authorization
Authentication verifies user identity while authorization determines what actions the authenticated user can perform. Both processes must work together seamlessly to protect application resources.
A secure architecture separates these concerns clearly. Authentication often uses tokens or sessions while authorization checks validate role permissions before executing protected actions.
Database Schema for Roles
An effective role based authentication system relies on a well designed database schema. Common tables include users roles permissions and role permission mappings. Relationships must be normalized to maintain scalability and performance.
Indexing foreign keys improves query speed. Structured data modeling prevents inconsistent permission assignments and supports long term maintainability as the application evolves.
3. Implementing Role Based Logic in Code
Middleware and Access Guards
Modern frameworks provide middleware or access guards to enforce authorization logic. Middleware intercepts incoming requests and validates the user role before allowing access to protected routes.
This approach centralizes access control. Instead of embedding permission checks throughout the codebase developers define reusable authorization layers that simplify maintenance and reduce security gaps.
Handling Dynamic Permission Checks
In advanced systems permissions may depend on contextual factors such as resource ownership. For example an editor may modify only content created by that editor. Dynamic checks ensure that roles are enforced intelligently rather than rigidly.
Developers should implement clear validation logic and consistent error handling. Denied access must return appropriate status codes without exposing internal system details.
4. Strengthening Security and Compliance
Principle of Least Privilege
The principle of least privilege is fundamental to role based authentication. Users should receive only the permissions required to perform assigned tasks. Limiting privileges reduces the potential impact of compromised accounts.
Periodic access reviews help maintain compliance. Administrators should audit role assignments regularly to remove unnecessary privileges and enforce updated policies.
Protecting Sensitive Endpoints
Sensitive endpoints such as administrative dashboards and financial records require strict authorization controls. Additional validation layers including multi factor authentication can enhance protection for high risk actions.
Logging access attempts and monitoring suspicious behavior strengthens overall security posture. Proactive monitoring helps detect misuse before it escalates into a breach.
5. Testing and Maintaining the Authorization System
Unit and Integration Testing
Thorough testing ensures that role based authentication functions as expected. Unit tests should verify permission checks while integration tests simulate real user workflows.
Testing must include negative scenarios. Attempting unauthorized actions confirms that restrictions are properly enforced and prevents accidental exposure of restricted resources.
Ongoing Maintenance and Scaling
As web applications grow new features often introduce additional roles and permissions. Developers must maintain clear documentation to avoid complexity and confusion.
Scalable role management systems support hierarchical roles or permission groups. Proper documentation and modular design make it easier to expand authorization capabilities without rewriting core logic.
Role based authentication is not simply a feature but a foundational security architecture for modern web applications. By designing structured roles implementing centralized authorization logic and enforcing the principle of least privilege organizations can protect sensitive data while maintaining operational efficiency.
A disciplined approach that includes database design middleware enforcement comprehensive testing and continuous monitoring ensures long term reliability. When implemented thoughtfully role based authentication strengthens both user experience and enterprise security standards.
Keywords
- Role based authentication
- Authorization
- Access control
- User roles
- Permissions
- Web applications
- Database schema
- Security architecture
- Middleware
- Principle of least privilege